In today’s corporate world, your accounts payable workflow can feel like the engine that keeps everything moving. You pay suppliers on time, you protect the supply chain, and you keep cash flow predictable. But here’s the uncomfortable truth: invoice fraud now sits right in the middle of that process, because scammers rarely hack their way in. They talk their way in, using social engineering to exploit routines, trust, and small gaps in approval steps.
The scary part is how normal it looks. A fake invoice can land in your inbox and match your vendor format, your tone, even your payment schedule. You approve it, the transfer goes out, and only later you notice the bank details were changed or the vendor never asked for anything. By then, it’s not just money you lose. You lose confidence, you lose time, and you risk awkward supplier disputes. And honestly, who wants to explain to management that a “routine payment” turned into a costly lesson?
If you operate in Malaysia, the pressure feels even higher because payments move fast and digital channels are everywhere. That speed is great until it helps fraud scale. So you need to treat invoice handling like a control point, not an admin chore, and you also need to respect local compliance realities: protect vendor and staff data under the Personal Data Protection Act 2010, and stay alert to the fact that fraud proceeds can trigger serious legal consequences under Malaysia’s anti money laundering law.
Key Takeaways
|

The Inner Workings of Malicious Billing Scams
To effectively combat deceptive billing practices, you need to understand how these schemes are orchestrated. Scammers do not simply send out random emails hoping for a lucky strike, modern scams are highly targeted, meticulously planned, and executed with a chilling level of professionalism.
The anatomy of a typical billing scam usually unfolds in three distinct phases: reconnaissance, infiltration, and execution. If you work in Malaysia, this awareness also supports safer handling of vendor and employee data under the Personal Data Protection Act 2010.
The Reconnaissance Phase
During the reconnaissance phase, scammers gather extensive intelligence about your business. They scour public records, corporate websites, and professional networking platforms like LinkedIn to identify key people in finance and procurement. They map out the hierarchy, noting who can approve payments and who processes them. Furthermore, they identify external partners, suppliers, and contractors.
By understanding the ecosystem you operate in, scammers can craft convincing narratives that match your regular activities.
The Infiltration Phase
Once the groundwork is laid, the infiltration phase begins.
This often involves Business Email Compromise (BEC), where a scammer accesses a legitimate account or spoofs an address to look like a trusted vendor or senior executive.
Through phishing emails with malicious attachments or links, they capture login credentials.
Once inside, they do not act immediately, instead, they monitor threads, study tone, and learn billing cycles and payment terms.That is why you need a clear vendor email verification process and a second channel confirmation routine.
The Execution Phase
The execution phase is where the trap is finally sprung.
With knowledge of your operations, the scammer intercepts a legitimate thread or starts a new one, posing as a known supplier. They submit a routine looking bill for services rendered or goods delivered.
The critical twist is a subtle request to update the supplier’s banking details, paired with a new account number and often a fabricated letterhead or forged signature. Because the request looks trusted and references real projects or purchase orders, AP processes the change, funds transfer, and the scam disappears.
What a Single Scam Can Break Inside Your Business
The consequences of falling victim to a billing scam extend far beyond the immediate loss of capital. While the direct financial hit is the most visible metric, the ripple effects can destabilize your business on multiple fronts. It is not just about money, it is about trust, time, and control.
Direct Financial Loss and Cash Flow Disruption
The most immediate and obvious impact is the loss of funds. Depending on the size of your business and the audacity of the scam, losses can range from a few thousand to several million dollars. For SMEs, one successful scam can wipe out a quarter’s profit margin or threaten solvency.
Furthermore, cash flow disruption can block payroll, rent, and legitimate vendor payments, triggering operational stress.That is why cash flow protection for AP teams cannot stay as a nice to have.
Reputational Damage and Loss of Trust
Beyond the balance sheet, reputational damage can be catastrophic.
If news of a breach becomes public, it can undermine the confidence of clients, investors, and stakeholders. Customers may question your ability to protect sensitive data, and investors may see weak controls as poor management.
Additionally, the relationship with the impersonated vendor can strain, because payment detail verification should have happened before the transfer. If you operate in Malaysia, PDPA discipline makes that trust conversation even more serious.
Regulatory and Legal Repercussions
In many jurisdictions, businesses face strict frameworks for data protection and financial controls. If a billing scam involves a data breach that exposed PII or sensitive corporate data, regulators can impose heavy penalties. Furthermore, legal exposure can follow if you fail fiduciary duties or fail to report incidents under statutory requirements. In Malaysia, you should treat incident handling as both a security task and a compliance task, not an informal cleanup.
Operational Paralysis and Remediation Costs
After a successful scam, operational paralysis often follows. Your finance team drops routine work to investigate, coordinate with banks, and liaise with authorities to recover funds. Remediation costs add up fast, external consultants, forensic audits, and new systems can compound the original loss. In Malaysia, rapid response matters, NSRC 997 exists to support quick action when you discover a scam.
A Clear View of the Most Common Invoice Fraud Types
To build effective defenses, you need to know the ways billing scams can show up.
Scammers keep evolving tactics, but most deceptive practices fall into a few primary categories.
You do not need panic, you need a practical checklist your team can follow.
Vendor Impersonation (Mandate Fraud)
This is arguably the most common and devastating form of billing scam.
As described in the execution phase above, scammers pose as an existing, trusted supplier.
They contact AP, usually via email, claiming banking details changed due to an audit, provider change, or restructuring.
They request that all future payments be routed to the new account. Because the request rides on trust, it often gets processed without independent verification, so you need a strict vendor bank account change policy.
Internal Fraud and Shell Companies
Not all threats come from outside, internal access can drive some of the worst outcomes.
A rogue employee with AP access creates a fictitious vendor profile, often called a shell company. This profile exists on paper with a fabricated name, address, and bank account controlled by the employee.
Then fake bills appear for intangible services like consulting or marketing research, which are hard to verify physically. Over time, money drains quietly unless you enforce strong vendor onboarding controls and periodic vendor master data reviews.
Duplicate Invoicing Scams
Duplicate billing can happen accidentally and maliciously. In a malicious context, a scammer or unethical vendor submits the same bill multiple times with small changes to the number or date. They rely on AP volume to slip duplicates past manual checks. If you lack automated duplicate invoice detection rules that flag matching amounts and PO numbers, you can pay twice. That is a preventable leak when your controls stay consistent.
Overbilling and Inflated Scams
In this scenario, a legitimate vendor inflates costs, adds unauthorized surcharges, or bills for items never delivered. It can look like a dispute, but when done systematically with intent to deceive, it becomes fraud. This type is insidious because the vendor is real and the baseline transaction is legitimate, so inflated charges hide in routine reviews. You catch it faster when you enforce invoice line item validation and three way matching discipline.
CEO Fraud (Executive Spoofing)
Closely related to vendor impersonation, CEO fraud involves spoofing a high ranking executive email. The scammer sends an urgent, confidential message to someone in finance to push an immediate transfer for a secret deal. Under pressure, the recipient bypasses standard verification and authorizes payment. You block this with an executive payment request verification workflow, plus a rule that urgency never overrides confirmation.
Red Flags That Help You Catch a Fraudulent Invoice Early
Scammers work hard to make fabricated documents look authentic, but small inconsistencies usually show up. Training AP to recognize red flags becomes a core part of your defense strategy.
You can build muscle memory with short refreshers and real examples.
Sudden Changes in Payment Details
The most glaring red flag is an unexpected request to change a supplier’s banking information. Legitimate businesses rarely change primary accounts, and when they do, they provide formal, verifiable documentation. Any email requesting routing updates, especially one that tells you to ignore previous instructions, should trigger an immediate halt. Verify independently before you move money, every time, even when the email looks perfect.
Induced Urgency and Emotional Manipulation
Scammers use psychological pressure to bypass logical controls.
They mark emails as Urgent, Confidential, or Overdue, then threaten late fees, legal action, or service suspension. This manufactured urgency aims to push you into skipping approval workflows.
Legitimate vendors may follow up, but professional requests still respect contractual terms and verification steps. That is why your team needs a clear process for handling urgent payment emails without breaking controls.
Discrepancies in Documentation and Formatting
A keen eye can often spot physical anomalies on a fabricated document. Look for low resolution logos, spelling and grammatical errors, or formatting that differs from previous submissions by the same vendor. Additionally, critical tax information must get close scrutiny. For example, when you review a VAT compliant invoice, make sure registration numbers match official records and align with what you already keep on file.
Irregular Communication Channels
Pay close attention to the sender’s email address. Fraudsters often use typosquatting, where they register a domain that looks almost identical to a legitimate vendor domain.
They may use rn instead of m, or swap dot com for dot co, and it still looks believable at a glance. If a vendor usually uses a portal or an account manager but suddenly emails from Gmail or Yahoo, treat it as a red alert and pause the payment.
Mismatched Amounts and Lack of Purchase Orders
Bills that arrive without a corresponding Purchase Order number, or that reference a PO that does not exist in your system, are highly suspect. Similarly, if the billed amount does not match the agreed contract price, you need to stop and verify. Watch for vague lines like professional services rendered without itemized detail. When details do not line up, do not release funds until you reconcile the invoice with your internal records.
Leveraging Technology to Combat Invoice Fraud
As fraudsters deploy increasingly sophisticated digital tools, you need to fight fire with fire.
Modernizing accounts payable through technology is no longer a luxury, it is a defensive move that reduces exposure. In Malaysia, cleaner digital records also support compliance readiness as LHDN rolls out e Invoice in phases. So the goal is not just speed, it is control you can repeat every time.
Accounts Payable Automation
Manual data entry is slow, error prone, and it creates gaps scammers can exploit. AP automation software digitizes the lifecycle from receipt to approval to payment. OCR extracts data from incoming documents, populates fields, and routes items through predefined workflows. When you reduce manual touchpoints, you reduce the chances that someone gets nudged into approving the wrong thing.
Advanced Matching Protocols
Automated AP systems can run fast multi point checks that manual review cannot maintain at scale. Implementing a three document invoice matching protocol reduces the risk of paying for goods never received or prices you never agreed to. It cross checks the invoice against the Purchase Order and the receiving report, then flags mismatches for review.
If a PO is missing or quantities do not align, the system blocks the transaction before any funds move.
Artificial Intelligence and Machine Learning
Newer financial software uses AI and ML to spot anomalies that humans miss. These models analyze historical payment patterns to build a baseline for each vendor. If a request breaks that baseline, like a sudden jump in amount or a strange billing time, the system flags it as high risk. Over time, the detection gets sharper because the model learns from new patterns and exceptions.
Digital Audit Trails and Secure Portals
Comprehensive accounting systems maintain tamper resistant audit trails. Every action gets recorded, who uploaded, who approved, who changed vendor details, and when it happened. Secure vendor portals with multi factor authentication add another barrier against impersonation attempts. If your records include personal data, PDPA discipline should shape how you store, access, and share it in daily operations.
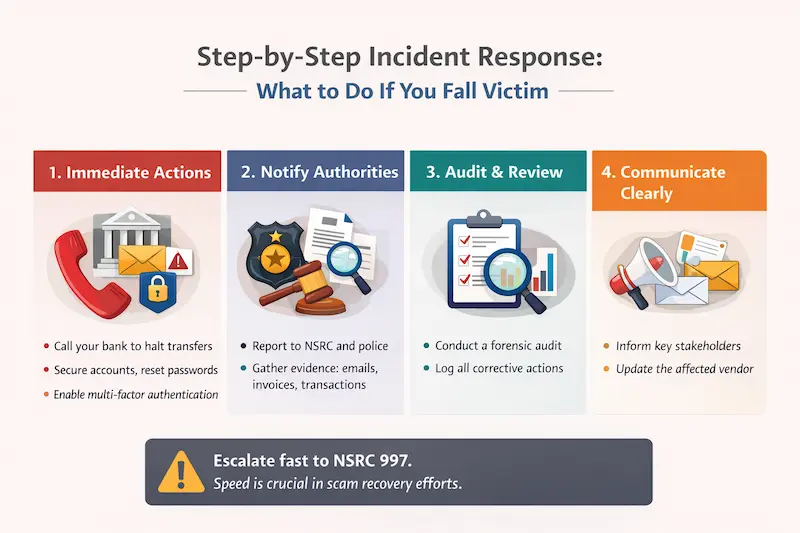
Step-by-Step Incident Response: What to Do If You Fall Victim
Despite preventative measures, breaches can still occur, and time matters. A swift response can decide whether you recover funds or absorb the full loss. In Malaysia, NSRC exists to speed up scam response coordination, so treat escalation as immediate, not optional. Do you already have a clear internal escalation path, or does everyone improvise in a crisis?
Immediate Containment and Financial Triage
The first step is to contact your bank immediately and share the transfer details.
If the transfer is recent, the bank may freeze funds or attempt a recall before money disperses further. At the same time, lock down access, reset passwords, and enforce multi factor authentication if you have not done it yet. If a compromised email account enabled the scam, cutting off access fast stops attackers from watching your response.
Engaging Law Enforcement and Legal Counsel
After you address the immediate financial risk, report the incident to the appropriate authorities with complete evidence. Provide email headers, fraudulent documents, and transfer records, because details drive investigation speed.
Consult legal counsel to manage reporting duties, especially if exposed emails include employee or customer data. If the case involves movement of criminal proceeds, Malaysia’s AMLA framework can become relevant to how the incident is handled and documented.
Post-Incident Auditing and Documentation
After the initial crisis, run a forensic audit to pinpoint how the breach happened. Was it weak access security, a rushed approval, or a control gap in vendor master data. Then document every correction so finance stays accurate, consistent, and audit ready.
If a transaction gets reversed or recovered, manage paperwork cleanly, including a Malaysia refund credit note, so the ledger stays compliant with local practice and reporting expectations.
Transparent Communication
Depending on the scale of the fraud, you may need to inform stakeholders and the impersonated vendor. It can feel uncomfortable, but transparency protects long term trust better than silence. Clear communication also helps the vendor take defensive steps on their side. Keep updates factual, focused on actions taken, and aligned with your internal and regulatory reporting needs.

Building a Human Firewall: Training and Awareness
Even the best technology fails when someone approves a payment under pressure. So you want your workforce to act like a human firewall, not a weak point. That means practical habits, clear playbooks, and permission to slow down when something feels off.
When security becomes everyone’s job, manipulation loses its easiest path.
Continuous Security Awareness Training
Annual generic training no longer matches how fast scams evolve. Keep training continuous, engaging, and tailored to AP, procurement, and finance roles. Teach not just the rules, but the why behind them, so people apply them under stress. When training ties to real workflows, it sticks and it prevents costly shortcuts.
Phishing Simulations and Practical Exercises
Simulated attacks train faster than theory because they mirror real decision moments. Send safe test emails and fake vendor requests to measure vigilance without blame. When someone slips, give immediate constructive feedback and targeted refreshers. These drills keep the threat fresh and expose process gaps that need tightening.
Establishing a Culture of Skepticism
The hardest change is cultural, but it pays off the most. Encourage healthy skepticism, even when a request looks like it came from a top executive or major vendor. Praise verification over speed, especially for urgent payment requests. When diligence gets rewarded, scammers lose the pressure tactics they depend on.
Industry-Specific Vulnerabilities and Use Cases
Invoice fraud hits every sector, but some industries carry extra exposure due to vendor churn and time pressure. So you should tailor controls to the way billing works in your environment, not a generic template. Use cases below show where scammers like to hide and why teams miss it. When you match controls to context, prevention becomes realistic instead of aspirational.
Construction and Real Estate
These industries rely on rotating subcontractors, independent tradespeople, and material suppliers. Scammers exploit project billing chaos by submitting invoices for materials never delivered or services never rendered. They know timelines pressure approvals, so verification can slip. Tighten proof of delivery and vendor change verification to reduce this exposure.
Healthcare and Pharmaceuticals
High volume procurement and urgent needs make healthcare a prime target. Scammers spoof medical vendors and push high value payments during stressful periods. Admin fatigue helps fraud blend into routine purchasing noise. Stronger approval gates for bank detail changes and unusual amounts make a big difference here.
Manufacturing and Logistics
Global supply chains bring cross border transactions, multiple currencies, and extended payment terms. Attackers may intercept vendor communications and alter transfer details to divert large payments. The fraud can hide until reconciliation, because shipments still move. Verify payment instruction changes out of band and treat bank details like sensitive data.
Strategic Implementation Steps for Fraud Prevention
Moving from reactive to proactive security needs a structured rollout.
You can strengthen controls without freezing operations, but you need clear steps and ownership. Focus on visibility, segregation of duties, and automated verification first.
Then standardize vendor master file controls so changes never slip through on email alone.
Conduct a Comprehensive AP Audit
Map every touchpoint in your payment lifecycle and identify where manual work creates gaps. Document who approves, who edits vendor data, and where handoffs break down.
Once you see the flow clearly, fixes become targeted instead of guesswork.
Enforce Strict Segregation of Duties
Make sure the person who creates or edits vendor records cannot also approve final payment release. This control blocks both internal fraud and external social engineering pressure. It sounds basic, but it stops a huge portion of real losses.
Deploy Automated Verification Systems
Integrate AP automation that enforces matching and approval rules consistently.
Automated checks reduce reliance on memory and manual attention during peak periods.
When exceptions appear, your team reviews only what needs review.
Establish a Vendor Master File Protocol
Require out of band verification for any change in bank details, routing numbers, or key contacts. Use known numbers and trusted contacts, not whatever appears in the request email. When you standardize this, scammers lose their favorite shortcut.
Advanced Practices and Next-Generation Defenses
As scammers adopt more sophisticated tools, defenses need to evolve too.
AI and ML can flag subtle anomalies like unusual billing frequency, unexpected amounts, or odd access patterns. Some teams explore blockchain and smart contracts to reduce silent tampering with vendor identities and payment routing history.
Combine predictive monitoring with zero trust habits and dynamic vendor authentication, and invoice fraud becomes far harder to land.
Conclution
Invoice fraud looks normal on purpose, that is what makes it dangerous. When a fake invoice matches your vendor style and timing, it can slip through even solid teams, then you pay the price in cash flow, trust, and operational disruption.
So treat AP like a control point, not admin work. Tighten verification for any change in payment details, reinforce human habits through training and simulations, and back it up with automation and traceable audit trails so you can block scams early and respond quickly if one still gets through.
Frequently Asked Questions About Invoice Fraud
-
What is invoice fraud in accounts payable (AP)?
Invoice fraud is when a scammer manipulates your AP process so money gets paid on a fake invoice or redirected to a fraudulent bank account. It often looks like a normal vendor request, which is why it’s so risky.
-
Why does invoice fraud look so legitimate?
Scammers mirror real vendor habits such as invoice layout, email tone, and payment timing. They want your team to treat it like a routine request and approve it without a second check.
-
What’s the typical pattern of a malicious billing scam?
Most scams follow a repeatable flow. The scammer studies your business, slips into communication channels, then triggers payment through a realistic invoice or a bank detail change.
-
What is Business Email Compromise (BEC), and why is it dangerous?
BEC is when a scammer accesses or impersonates a legitimate email account to send convincing payment-related instructions. It’s dangerous because the request appears to come from a trusted vendor or executive, so people skip verification.